Prepare and Measure Quantum Digital Signature
Functionality Description
Digital Signatures (QDS) allow the exchange of classical messages from sender to multiple recipients, with a guarantee that the signature has come from a genuine sender. Additionally, it comes with the properties of (i) transferability i.e. messages with DS can be forwarded from one recipient to another such that DS is verifiable to have come from the original sender, (ii) non-repudiation i.e at any stage after sending the message to one recipient, sender cannot deny having sent the message and corresponding DS, and (iii) unforgeability i.e. a dishonest recipient cannot alter or fake the sender's DS and forward it to other recipients successfully. For simplicity, most protocols take into account the case of one sender and two recipients (Seller, buyer and verifier) exchanging single-bit classical messages.
Such protocols require parties to prepare and measure quantum states instantly without having to store them, hence the name, Prepare and Send QDS.
Tags: Multi Party (three), Quantum Enhanced Classical Functionality, Specific Task, Quantum Digital Signature, Quantum Digital Signature with Quantum Memory, Measurement Device Independent Quantum Digital Signature (MDI-QDS)
Requirements
- Network Stage: Prepare and Measure
- Method: Single quantum state preparation and measurement in two different bases
- Relevant Network Parameters:
- Benchmark values: Length of the keys(L): , Verification threshold per qubit ():, Signing threshold per qubit():, time, scalability, no. of rounds, time, distance, scalability, no. of rounds, threshold values numbers, length of the key
Use Case
Online Transactions, Signing Marksheets
Example:
Outline
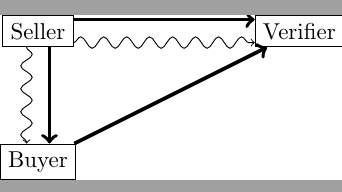
Quantum Digital Signature (QDS) protocols can be separated into two stages: the distribution stage, where quantum signals (public keys) are sent to all recipients, and the messaging stage, where classical messages are signed, sent and verified. Here, we take the case of three parties, one sender (referred to as seller) and two receivers (buyer and verifier) sharing a one bit message. Distribution phase can be divided into the following steps:
- Key Distribution: Seller generates her (public key,private key) pair and shares the public key with both receivers in this step. For each possible message (0 or 1), she generates two identical sequences/copies (one for each receiver per possible message) of randomly chosen BB84 ∈ {0,1,+,−} states. The sequence of states is called quantum public key and its classical description, private key. She then sends copies of each quantum public key to the receivers while keeping both the private keys secret to herself. At the end of this step, seller has two private keys, one for each possible message. Similarly, each receiver has two quantum public keys, one for each possible message.
- State Elimination: Receivers store their classical records of the quantum public keys in this step. For each quantum public key received, a receiver randomly chooses X or Z basis for each qubit and measures. Whatever outcome he gets, the receiver is certain that seller could not have generated a state orthogonal to his outcome. So, he records the state orthogonal to his outcome as the eliminated signature element. Such measurement is called ’Quantum State Elimination’. The sequence thus generated by measurement of all the qubits in a public key is called receiver’s eliminated signature for the respective quantum public key. Thus, each receiver finally has two eliminated signatures, one for each possible message.
- Symmetrisation: The two receivers exchange half of their randomly chosen eliminated signature elements. This prevents a dishonest seller succeed in cheating by sending dissimilar public keys to the receivers. Thus ends the distribution phase.
Similarly, Messaging Phase is divided into the following steps:
- Signing: Seller sends desired classical one bit message and the corresponding private key to the desired receiver (called buyer). Buyer compares the private key with his eliminated signature for the corresponding message and counts the number of mismatches (eliminated signature element in seller’s private key).
- Transfer: Buyer forwards the same message and private key to the other receiver (called verifier) who compares it with his eliminated signature for this message.
Properties
- The protocol-
- involves three parties (Seller, Buyer, Verifier) exchanging one-bit classical messages.
- Requires BB84 QKD setup, authenticated quantum and classical channels
- assumes maximum number of participating parties are honest. In the present case at least two parties are honest.
- provides information-theoretic security
- provides security against repudiation, i.e. the probability that seller succeeds in making buyer and seller disagree on the validity of her sent quantum signature decays exponentially with L, as stated by the formula .
- provides security against forgery, i.e. any recipient (verifier) with high probability rejects any message which was not originally sent by the seller herself. Forging probability is given by the formula, , where is 3/8 (calculated using uncertainty principle).
Pseudo Code
- Notations Used:
- L: Length of keys used
- : Threshold value for signing
- : Threshold value for verification
- : Quantum Public key for message k
- : Classical Private key for classical one-bit message k
- : Classical description of qubit in Failed to parse (SVG (MathML can be enabled via browser plugin): Invalid response ("Math extension cannot connect to Restbase.") from server "https://wikimedia.org/api/rest_v1/":): {\displaystyle |\psi^k\rangle}
- Failed to parse (SVG (MathML can be enabled via browser plugin): Invalid response ("Math extension cannot connect to Restbase.") from server "https://wikimedia.org/api/rest_v1/":): {\displaystyle B^m} : Buyer's Eliminated Signature for message m
- Failed to parse (SVG (MathML can be enabled via browser plugin): Invalid response ("Math extension cannot connect to Restbase.") from server "https://wikimedia.org/api/rest_v1/":): {\displaystyle V^m} : Verifier's Eliminated Signature for message m
- Failed to parse (SVG (MathML can be enabled via browser plugin): Invalid response ("Math extension cannot connect to Restbase.") from server "https://wikimedia.org/api/rest_v1/":): {\displaystyle b^k_l} : Buyer’s random bit to determine the measurement basis of Failed to parse (SVG (MathML can be enabled via browser plugin): Invalid response ("Math extension cannot connect to Restbase.") from server "https://wikimedia.org/api/rest_v1/":): {\displaystyle l^{th}} qubit in Failed to parse (SVG (MathML can be enabled via browser plugin): Invalid response ("Math extension cannot connect to Restbase.") from server "https://wikimedia.org/api/rest_v1/":): {\displaystyle |\psi^k\rangle}
- Failed to parse (SVG (MathML can be enabled via browser plugin): Invalid response ("Math extension cannot connect to Restbase.") from server "https://wikimedia.org/api/rest_v1/":): {\displaystyle v^k_l} : Verifier’s random bit to determine the measurement basis of Failed to parse (SVG (MathML can be enabled via browser plugin): Invalid response ("Math extension cannot connect to Restbase.") from server "https://wikimedia.org/api/rest_v1/":): {\displaystyle l^{th}} qubit in Failed to parse (SVG (MathML can be enabled via browser plugin): Invalid response ("Math extension cannot connect to Restbase.") from server "https://wikimedia.org/api/rest_v1/":): {\displaystyle |\psi^k\rangle}
- Failed to parse (SVG (MathML can be enabled via browser plugin): Invalid response ("Math extension cannot connect to Restbase.") from server "https://wikimedia.org/api/rest_v1/":): {\displaystyle m_{b^k_l}} : measurement outcome of Failed to parse (SVG (MathML can be enabled via browser plugin): Invalid response ("Math extension cannot connect to Restbase.") from server "https://wikimedia.org/api/rest_v1/":): {\displaystyle b^k_l}
Stage 1 Distribution
- Input L
- Output Seller: Failed to parse (SVG (MathML can be enabled via browser plugin): Invalid response ("Math extension cannot connect to Restbase.") from server "https://wikimedia.org/api/rest_v1/":): {\displaystyle \{\beta^0_1,...,\beta^0_L\},\{\beta^1_1,...,\beta^1_L\}}
; Buyer: Failed to parse (SVG (MathML can be enabled via browser plugin): Invalid response ("Math extension cannot connect to Restbase.") from server "https://wikimedia.org/api/rest_v1/":): {\displaystyle B^0,B^1}
; Verifier: Failed to parse (SVG (MathML can be enabled via browser plugin): Invalid response ("Math extension cannot connect to Restbase.") from server "https://wikimedia.org/api/rest_v1/":): {\displaystyle V^0,V^1}
- Key Distribution:
- For k = 0,1
- Seller prepares quantum public key Failed to parse (SVG (MathML can be enabled via browser plugin): Invalid response ("Math extension cannot connect to Restbase.") from server "https://wikimedia.org/api/rest_v1/":): {\displaystyle |\psi^k\rangle=\bigotimes^L_{l=1}|\beta^k_l\rangle} , where Failed to parse (SVG (MathML can be enabled via browser plugin): Invalid response ("Math extension cannot connect to Restbase.") from server "https://wikimedia.org/api/rest_v1/":): {\displaystyle \beta^k_l\in_R \{0,1,+,-\}}
- She sends Buyer (k,Failed to parse (SVG (MathML can be enabled via browser plugin): Invalid response ("Math extension cannot connect to Restbase.") from server "https://wikimedia.org/api/rest_v1/":): {\displaystyle |\psi^k\rangle} )
- She sends Verifier (k,Failed to parse (SVG (MathML can be enabled via browser plugin): Invalid response ("Math extension cannot connect to Restbase.") from server "https://wikimedia.org/api/rest_v1/":): {\displaystyle |\psi^k\rangle} )
- State Elimination:
- For k = 0,1
- For l = 1,2,...,L
- Buyer chooses Failed to parse (SVG (MathML can be enabled via browser plugin): Invalid response ("Math extension cannot connect to Restbase.") from server "https://wikimedia.org/api/rest_v1/":): {\displaystyle b^k_l \epsilon_R {0,1}}
- If Failed to parse (SVG (MathML can be enabled via browser plugin): Invalid response ("Math extension cannot connect to Restbase.") from server "https://wikimedia.org/api/rest_v1/":): {\displaystyle b^k_l=0} , Buyer measures his qubit in X basis Failed to parse (SVG (MathML can be enabled via browser plugin): Invalid response ("Math extension cannot connect to Restbase.") from server "https://wikimedia.org/api/rest_v1/":): {\displaystyle \{|+\rangle,|-\rangle\}}
- If Failed to parse (SVG (MathML can be enabled via browser plugin): Invalid response ("Math extension cannot connect to Restbase.") from server "https://wikimedia.org/api/rest_v1/":): {\displaystyle b^k_l=0} , Buyer measures his qubit in Z basis Failed to parse (SVG (MathML can be enabled via browser plugin): Invalid response ("Math extension cannot connect to Restbase.") from server "https://wikimedia.org/api/rest_v1/":): {\displaystyle \{|0\rangle,|1\rangle\}}
- return Failed to parse (SVG (MathML can be enabled via browser plugin): Invalid response ("Math extension cannot connect to Restbase.") from server "https://wikimedia.org/api/rest_v1/":): {\displaystyle m_{b^k_l}}
- Failed to parse (SVG (MathML can be enabled via browser plugin): Invalid response ("Math extension cannot connect to Restbase.") from server "https://wikimedia.org/api/rest_v1/":): {\displaystyle B^k_l=1-m_{b^k_l}}
- For l = 1,2,...,L
- Verifier repeats steps 2(a)-2(b) with randomly chosen basis Failed to parse (SVG (MathML can be enabled via browser plugin): Invalid response ("Math extension cannot connect to Restbase.") from server "https://wikimedia.org/api/rest_v1/":): {\displaystyle v^k_l} to get his eliminated signature elements Failed to parse (SVG (MathML can be enabled via browser plugin): Invalid response ("Math extension cannot connect to Restbase.") from server "https://wikimedia.org/api/rest_v1/":): {\displaystyle V^k_l}
- Symmetrisation
- For k = 0,1
- Buyer chooses IFailed to parse (SVG (MathML can be enabled via browser plugin): Invalid response ("Math extension cannot connect to Restbase.") from server "https://wikimedia.org/api/rest_v1/":): {\displaystyle \subset_R\{1,2,...,L\}, |I|=[L/2]}
- Failed to parse (SVG (MathML can be enabled via browser plugin): Invalid response ("Math extension cannot connect to Restbase.") from server "https://wikimedia.org/api/rest_v1/":): {\displaystyle \forall i\epsilon I} , Buyer sends Verifier Failed to parse (SVG (MathML can be enabled via browser plugin): Invalid response ("Math extension cannot connect to Restbase.") from server "https://wikimedia.org/api/rest_v1/":): {\displaystyle (k,i,b^k_i,B^k_i)}
- Verifier chooses JFailed to parse (SVG (MathML can be enabled via browser plugin): Invalid response ("Math extension cannot connect to Restbase.") from server "https://wikimedia.org/api/rest_v1/":): {\displaystyle \subset_R\{1,2,...,L\}, |J|=[L/2]}
- Failed to parse (SVG (MathML can be enabled via browser plugin): Invalid response ("Math extension cannot connect to Restbase.") from server "https://wikimedia.org/api/rest_v1/":): {\displaystyle \forall j\epsilon J} , Verifier sends Buyer Failed to parse (SVG (MathML can be enabled via browser plugin): Invalid response ("Math extension cannot connect to Restbase.") from server "https://wikimedia.org/api/rest_v1/":): {\displaystyle (k,j,v^k_j,V^k_j)}
- Failed to parse (SVG (MathML can be enabled via browser plugin): Invalid response ("Math extension cannot connect to Restbase.") from server "https://wikimedia.org/api/rest_v1/":): {\displaystyle \forall j\epsilon J} Buyer replaces Failed to parse (SVG (MathML can be enabled via browser plugin): Invalid response ("Math extension cannot connect to Restbase.") from server "https://wikimedia.org/api/rest_v1/":): {\displaystyle B^k_l=V^k_l}
- Failed to parse (SVG (MathML can be enabled via browser plugin): Invalid response ("Math extension cannot connect to Restbase.") from server "https://wikimedia.org/api/rest_v1/":): {\displaystyle \forall i\epsilon I} Verifier replaces Failed to parse (SVG (MathML can be enabled via browser plugin): Invalid response ("Math extension cannot connect to Restbase.") from server "https://wikimedia.org/api/rest_v1/":): {\displaystyle V^k_l=B^k_l}
- For k = 0,1
Stage 2 Messaging
- Input Seller: Message m, Private Key for m: Failed to parse (SVG (MathML can be enabled via browser plugin): Invalid response ("Math extension cannot connect to Restbase.") from server "https://wikimedia.org/api/rest_v1/":): {\displaystyle \{\beta^m_1,...,\beta^m_L\}}
- Output Buyer: accept or abort, Verifier: accept or abort
- Signing: ’mismatch’ is when Buyer finds an eliminated signature element in Seller’s private key
- Seller sends Buyer (m,Failed to parse (SVG (MathML can be enabled via browser plugin): Invalid response ("Math extension cannot connect to Restbase.") from server "https://wikimedia.org/api/rest_v1/":): {\displaystyle \{\beta^m_1,...,\beta^m_L\}} )
- For l = 1,2,..,L
- Buyer counts the number of mismatches (Failed to parse (SVG (MathML can be enabled via browser plugin): Invalid response ("Math extension cannot connect to Restbase.") from server "https://wikimedia.org/api/rest_v1/":): {\displaystyle B^m_l=V^m_l} ) and returns Failed to parse (SVG (MathML can be enabled via browser plugin): Invalid response ("Math extension cannot connect to Restbase.") from server "https://wikimedia.org/api/rest_v1/":): {\displaystyle S_b}
- If Failed to parse (SVG (MathML can be enabled via browser plugin): Invalid response ("Math extension cannot connect to Restbase.") from server "https://wikimedia.org/api/rest_v1/":): {\displaystyle S_b < s_aL/2} , Buyer accepts m else he aborts
- Transfer
- Buyer sends Verifier (m,Failed to parse (SVG (MathML can be enabled via browser plugin): Invalid response ("Math extension cannot connect to Restbase.") from server "https://wikimedia.org/api/rest_v1/":): {\displaystyle \{\beta^m_1,...,\beta^m_L\}} )
- For l = 1,2,....,L
- Verifier counts the number of mismatches (Failed to parse (SVG (MathML can be enabled via browser plugin): Invalid response ("Math extension cannot connect to Restbase.") from server "https://wikimedia.org/api/rest_v1/":): {\displaystyle V^m_l=B^m_l} ) and returns Failed to parse (SVG (MathML can be enabled via browser plugin): Invalid response ("Math extension cannot connect to Restbase.") from server "https://wikimedia.org/api/rest_v1/":): {\displaystyle S_v}
- If Failed to parse (SVG (MathML can be enabled via browser plugin): Invalid response ("Math extension cannot connect to Restbase.") from server "https://wikimedia.org/api/rest_v1/":): {\displaystyle S_v < s_vL/2} , Verifier accepts m else he aborts
Discussion
- Theoretical Papers
- WDKA (2015) above example
- GC-QDS (2001) uses quantum one way function f(); Private keys: classical input x, Public keys: quantum output f(x). Requires quantum memory, quantum one way function, authenticated quantum and classical channels, SWAP Test (universal quantum computer). Unconditionally Secure. Network Stage: Quantum Memory
- ACJ (2006) discusses coherent states comparison with a QDS scheme outlined in the last section. Protocol uses the same protocol as (2) but replaces qubits with coherent states, thus replacing SWAP-Test with Coherent State Comparison. Additionally, it also requires quantum memory, authenticated quantum and classical channels, multiports. Unconditionally Secure, Network Stage: Quantum Memory
- DWA (2013) first QDS scheme without quantum memory based on (3). Requires Coherent States, authenticated quantum and classical channels, multiports, Unambiguous State Discrimination (USD) (State Elimination), no symmetrisation required. Unconditionally Secure. Network Stage: Prepare and Measure
- AL (2014) Establishes coherent state mapping of (2). Replaces SWAP Test with beam splitters. Uses Unambiguous State Discrimination (USD) (State Elimination). Requires Phase encoded Coherent states, Balanced Beam Splitters. No explicit security proof provided. Network Stage: Prepare and Measure
- AWA (2015) security proof for generalisation of WDKA (2015) and DWA (2013) to more than two recipients case.
- YFC (2016) first QDS scheme without authenticated (trusted) quantum channels. Demonstrates one protocol with two implementation, two copies of single photon method and decoy state method. First uses single qubit photons in three bases; Private key: classical description of states, Public key: pair of non-orthogonal states in any two of the three bases. Requires authenticated classical channels, polarisation measurement in three bases, Unambiguous State Discrimination (USD) (State Elimination), uses quantum correlations to check authentication. Decoy State method uses phase-randomised weak coherent states, 50:50 Beam Splitter (BS), Unconditionally Secure Network Stage: Prepare and Measure.
- AWKA (2015) QDS scheme without authenticated quantum channels using parameter estimation phase. Uses a Key Generations Protocol (KGP) where noise threshold for Seller-Buyer and Seller-Verifier is better than when distilling secret key from QKD. Seller sends different key to Buyer and Verifier using KGP. This anamoly is justifiable due to symmetrisation.Requires authenticated classical channels, decoy state BB84 QKD setup. Unconditionally Secure Network Stage: Prepare and Measure.
- MH (2016) security proof for generalisation of AWKA (2015) to more than two recipients case.
- WCRZ (2015) demonstrates sending multi-bit classical messages using AWKA (2015) or other similar protocols.
- SWZY (2017) Discusses an attack and suggests corrections on existing QDS scheme using single qubit rotations. Protocol uses rotation, qubits, one-way hash function; Private keys: angle of rotation, Public keys: string of rotated quantum states. Requires random number generator, one-way hash function, quantum memory, key distribution. Computationally Secure, Third Network Stage (Quantum Memory)
- Experimental Papers